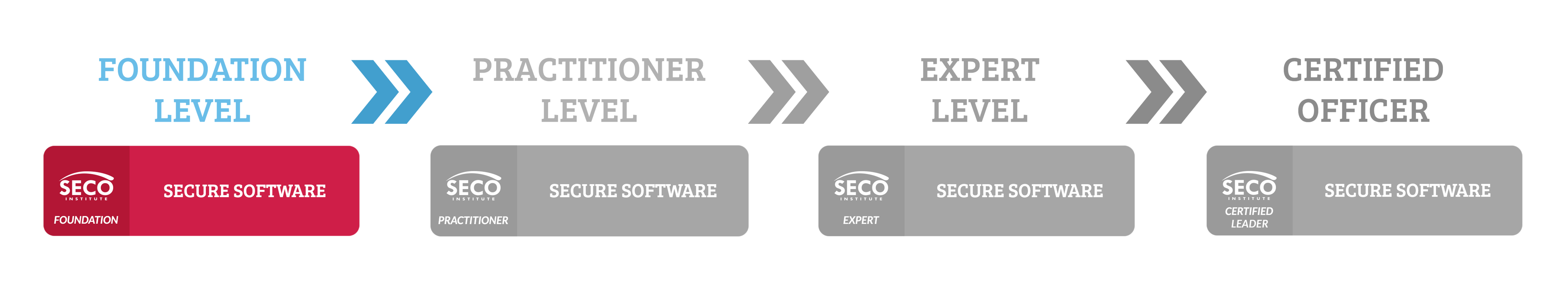
Secure Programming Foundation (S-SPF)
Hands-on secure software development fundamentals EnrollBook as in-companyWhat will you learn?
- 9Understand the Secure Software Development Life Cycle (SSDLC) and grasp the fundamental principles of secure design, threat modelling and secure coding;
- 9Understand what coding mistakes lead to insecure software and how vulnerabilities are exploited by hackers;
- 9Analyse code, identify common mistakes that may lead to security problems, and verify the security of code;
- 9Practice threat modelling, identify threats and determine mitigations;
- 9Use threat modelling to design ideal code constructs to achieve security goals.
Information
- 3 course days, 1pm – 5.30pm CEST
- 20,5 hours of self-study
- R1 CPE credit per study hour
Secure Programming Foundation Course – Hands-on secure software development fundamentals
Our Secure Programming Foundation course gives you an intensive hands-on introduction to secure software development. In this course, you will learn what programming errors can lead to software vulnerabilities, how these errors are exploited by attackers, and how you can prevent software flaws that enable cyber attacks.
Developed by practicing security experts with extensive experience in software security, the course offers an ideal combination of secure software design principles, threat modelling practice, TryHackMe lab exercises, interactive discussions and fresh insights from the industry. This secure software development training benefits software developers as well as security professionals, (aspiring) software engineers and auditors, and future lead developers, architects and managers.
Prerequisites to joining this Secure Programming Foundation course
Secure Programming Foundation requires coding skills and a basic understanding of the software development life cycle. To succeed in this course, you should be able to use at least one programming language and be familiar with the most common software development models.
Is this Secure Programming Foundation course for you?
This course equips you with an in-depth understanding of common software vulnerabilities and best-practice countermeasures to develop secure software. The Secure Programming Foundation course and certification are ideal for your skills and career advancement if you are a:
- Software developer aspiring to build secure coding knowledge and programming skills;
- Software development manager, software architect, software auditor, or other professional who needs to work with secure programmers;
- Security professional who needs to understand application security from a development perspective.
What is included in this Secure Programming Foundation course?
- Official SECO-Institute course materials developed by practicing security experts;
- Training from passionate instructors who are active in the security industry;
- Access to the SECO-Institute’s lab environment
- Practice exam and exam syllabus so you can fully prepare for your certification exam;
- Certification exam voucher;
- Access to the (S)ECO-system, the SECO-Institute’s professional community website where you will find additional resources and exclusive knowledge events.
Why train to be a secure programmer with Security Academy Online?
Security Academy Online courses are rich with hands-on practice and equip you with actionable knowlegde and skills. We only work with freelance senior instructors who have extensive experience in the security industry and have guided many customers in their efforts to build a solid secure software development practice. Our trainers’ in-depth security expertise and strong development background guarantees that in this course you will not just understand the risks of insecure software, but also learn how to actually produce secure code. Our trainers have gone through a scrutinous accreditation process testing their subject-matter expertise as well as their communication and presentation skills to ensure you will have a powerful and pleasant learning experience. When not consulting or teaching, you will find them presenting at international cyber security conferences and supporting non-profit community-driven projects, sharing their knowledge and expertise for the greater good.
Secure Programming Foundation Course Modules
Module 1: The fundamentals of secure software
The first part of the course introduces you to why secure programming is important and how to build a business case for secure development. This section also gives you an overview of the conditions needed to succeed in secure development. After discussing the business case and the necessary preconditions, we will discuss the Secure Software Development Life Cycle (SSDLC). The module concludes with an overview of the properties that make software secure or open it up to attacks if not implemented properly.
The case for software security
There is no place to hide security issues. They will be found and exploited if you don’t fix them in time. By postponing this work and creating technical/security debt, you will only make things harder on yourself and increase the costs of something you will have to do eventually anyway. And if you don’t fix your issues, you will be held accountable. Laws are getting tougher and society is raising its expectations of what it thinks is your responsibility. In the end it makes sense business-wise to improve your security stance. Especially when you take into account that the cost of security breaches always is higher than anticipated and is ever increasing.
Setting the stage for success
There is no simple recipe for making software secure. You need to build an environment that supports secure development. This means creating a culture where security is important and where this importance is reflected in communications and in the decisions that are made. It also means building and maintaining the right knowledge base and skill set to become and stay good at it. Once that is in place you need to adopt some best practices to ensure you get good results. Think of reducing complexity, practising defence in-depth, making maintenance easy, preparing for changes, and evaluating third-party code before incorporating it in your work, a.o..
Secure development models
Realise what it takes to “do” secure development by understanding and implementing the Secure Software Development Life Cycle. Even if you have adopted DevOps, this is still the basis for achieving success.
What makes software (in)secure?
There are many many ways in which software can be either secure or open to attacks. Using SECO’s Application Security Framework, a coherent overview of all these aspects of secure software is given. Because almost all software that processes data will have some link to databases, a short overview of database security is included in this section.
Module 2: Workshop Threat Modelling
Module 2 will help you understand what threat modelling is, what it aims to achieve, and how it is done. This part will be concluded with a workshop wherein we will make a threat model of a new service that our simulated company (Bicsma) wants to introduce to the market.
In this module, we will discuss all four steps of the threat modelling process:
- Modelling the system
- Modelling the threats to the system
- Mitigating the threats that were found
- Verifying the threat model
Module 3: Secure Coding
The third and last part of the course is pure hands-on practice. We will review a number of common security issues using practical examples. Think of:
- Input validation
- Buffer overruns
- Exception handling
- Command injection
- Integer overflows
- Information disclosure
- Race conditions
Practice Exam
On your last course day, you will take a practice exam. After taking the practice exam, you will have the opportunity to discuss your answers with the group. This will help you familiarise yourself with the exam format, identify your strengths and weaknesses, and improve your exam technique. After completing the course, you will be fully prepared to take your SECO Secure Programming Foundation (S-SPF) certification exam.
Secure Programming Foundation Certification Exam
The certification exam is conducted by the SECO-Institute, Europe’s leading security and continuity certification body. The exam voucher is included in the course fee, but you need to schedule your exam with the SECO-Institute. Upon successful completion of the exam, you will receive an exam certificate and an invitation to register your official SECO-Secure Programming Foundation (S-SPF) certification title free of charge. By activating your certification title, you will become a certified professional in your field and you will receive a shareable digital badge to verify your competence to clients, employers and fellow professionals.
Exam information
- Exam language: English
- Exam delivery: Online exam with remote proctoring
- Exam format: 40 multiple-choice questions
- Duration: 60 minutes
Why earn a SECO-Secure Programming Foundation (S-SPF) certificate?
Secure Programming Foundation equips you with the knowledge and skills you need to lay the foundations of a career as a secure software developer, software engineer or software auditor. By passing the SPF certification exam and earning a SECO-Secure Programming Foundation (S-SPF) certificate, you verify that you know what programming errors can lead to software vulnerabilities, how these errors are exploited by attackers, and how you can prevent software flaws that enable cyber attacks.
In particular, an S-SPF certificate demonstrates your ability to:
- Understand the importance of security in the software lifecycle and the logic behind industry-approved secure development principles;
- Understand web application attack surfaces and trust boundaries;
- Understand the workings of HTTP requests and header injection;
- Understand password authentication vulnerabilities and effective countermeasures;
- Understand the security implications of session management and identify effective countermeasures against session fixation;
- Identify countermeasures against cross-site request forgery (CSRF) and clickjacking attacks;
- Identify countermeasures against injection attacks;
- Identify countermeasures against buffer overflows;
- Identify countermeasures against cross-site scripting (XSS);
- Identify countermeasures against file upload attacks;
- Identify countermeasures against character encoding vulnerabilities;
- Understand privilege escalation and list relevant mitigation techniques;
- Secure products by hardening and vulnerability scanning;
- Understand how to prevent side-channel attacks;
- Understand how to prevent DoS attacks;
- Understand the importance of good error handling practices;
- Understand the security risks involved in logging;
- Understand symmetric and asymmetric cryptography, Man-in-the-Middle attacks, and the pitfalls in SSL/TLS and HTTPS certificates.
- Explain how security requirements can/should be identified;
- Perform simple threat modelling exercises and identify security requirements for a system.
What are the benefits of an S-SPF certificate?
An S-SPF certificate demonstrates that you have a solid understanding of common software vulnerabilities and best-practice countermeasures. If you are considering a career in secure software development or software auditing, these competences are essential to get you started.
Authors & Lead Trainers
Register now
In-company training tailored to your needs
Schedule this training as in-company. Upskill your entire team in the most cost-effective way!